QUESTIONS
SECTION A: (40 MARKS)
Answer ALL the questions in this section in the space provided.
-
- A computer laboratory should be constantly kept dust and smoke free. Specify two effects that dust would have on the operation of computers.
- Why should you first switch on the UPS before switching on the system unit and the monitor?
- Explain the meaning of backup.
- State the following types of transcription errors.
- 3455 instead of 3456....
- Smith instead of simth.
-
- State three ways used to represent a negative number.
- Perform the following binary arithmetic giving the answer in decimal notation.
1110.0111 + 1101001.011
- Distinguish between data privacy and data integrity as used in computing.
- Differentiate between a primary key and a foreign key while designing a database.
- Distinguish between 'count' and 'countif" functions as used in spreadsheets.
- Match the following statements with repeater, router or a bridge.
STATEMENT DEVICE Operates at data link layer Determine the best path for data to follow Regenerates signals Fowards everything which it doesn't recognize - Explain the impact of Information Technology on organization in each of the following areas.
- Competition.
- Pace of growth
- List two roles performed by system analyst.
- Explain the following internet related terms.
- Sign IN
- Search engine
- Surf
- Sign up
- In Kenya Tea Packers Company, several people are employed as record clerks, typists and messenger. The company intends to introduce a computerized system in all the departments. Suggest three reasons that would make workers unhappy with the new system.
- State two magnetic Storage devices.
- State three functions of Central Processing Unit.
- For each of the following file organization methods, state an appropriate storage medium:
- Serial
- Random
SECTION B: (60 MARKS)
Answer question 16 (compulsory) and any other THREE questions from this section.
-
- Study the flowchart below and answer the questions that follows.
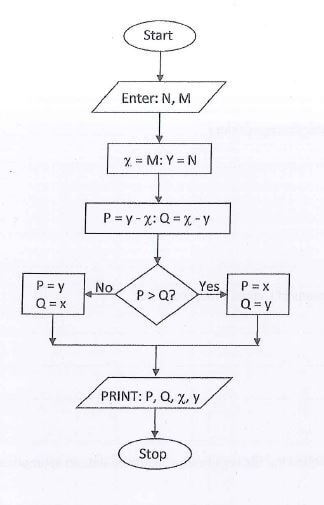
- State the name of the control structure shown in the flowchart.
- Assuming the user keys in 8 and 14 when prompted to enter the values for M and N respectively, determine the printed values of P, Q, x and y.
- Write the pseudocode that would be used in place of the flowchart
- What is the difference between looping and selection.
- Name the stage of program development cycle when:
- A user guide would be written.
- A programmer dry-runs the code.
- System charts would be drawn.
- Study the flowchart below and answer the questions that follows.
-
- What is Virtual reality?
- Explain the following interactive sensory equipment used in virtual reality.
- Head gear.
- Body suit.
-
- What is Artificial Intelligence?
- State and explain three components of an experts system.
- Most computerized security systems make use of Biometric analysis, name three physical features of human beings that can be considered in this analysis.
-
- Explain two coding schemes used in data representation techniques.
- Using one's and two's complement work out 14-9.
- One's complement.
- Two's complement.
- Work out the hexadecimal equivalent of 1011111000112
- Identify the following types of ports
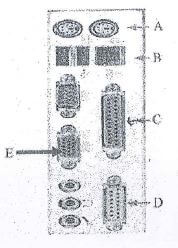
A....................................................
B....................................................
C....................................................
D....................................................
F....................................................
-
- Explain two functions of an operating system,
- Explain the following terms as used in disk management using operating system:
- Disk defragmentation.
- Disk clean up.
- What will happen if you attempt to delete a folder while a file contained in it is Open?
- State two properties that an operating system displays about a file.
- Give four advantages of storing files in folders,
-
- The diagram below shows four common network topologies A, B, C and D.
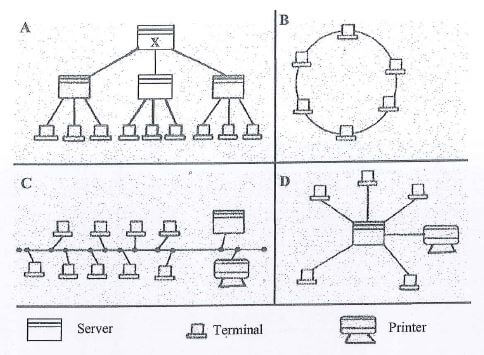
- Name the network topologies labeled A, B, C and D.
- Explain what happens if server X in topology A fails.
- List two problems associated with network topology B.
- List two disadvantage associated with network topology labeled D.
- Differentiate between Internet and World Wide Web.
- Describe the following network services and identify their applications.
- Voice mail.
- Video conferencing.
- The diagram below shows four common network topologies A, B, C and D.
Download Computer Studies Paper 1 Questions - Mangu High School Mock Exams 2022.
Tap Here to Download for 50/-
Get on WhatsApp for 50/-
Why download?
- ✔ To read offline at any time.
- ✔ To Print at your convenience
- ✔ Share Easily with Friends / Students
