QUESTIONS
SECTION A – 40MKS
- State two reasons for the increases use of lap top computers in government offices. (2mks)
- Computer network technicians prefer to use command – like based operating system when configuring networks. State three reasons for the preference. (3mks)
- State three measures that should be put in place in a computer laboratory to safeguard user’s health. (3mks)
- State three ways in which barcode readers may be used in schools. (3mks)
- State three advantages of flat panel monitors over cathode ray tube monitor as used in computers. (3mks)
- State three possible reasons for the extinction of daisy wheel printers in the market. (3mks)
- State three ways in which an operating system secures a computer system. (3mks)
- A law firm prefers to use a hard copy output over soft copy output when handling documents for legal matters. State two reasons for this preference. (2mks)
- State the function of each of the following features in a word processor application
- Thesaurus (1mk)
- Comment (1mks)
- With the aid of an example, explain the term multi level list as used in word processing. (3mks)
- Distinguish between real time operating system and distributed operating system. (3mks)
- State fair computer based careers introduced as a result of computerized data processing methods at the airport. (2mks)
- Explain the function of a protect sheet feature in a spreadsheet program. (2mks)
- In a spreadsheet, the formula = if (AL> 10, al*77, Al*50) is entered in a cell. Interpret the results. (3mks)
- State a state in system development life cycle where each of the following activities is carried out.
- Identifying the technologies that may be used in a proposed system. (1mk)
- Identifying shortcomings of a system. (1mk)
- Preparing the system migration plan. (1mk)
SECTION B. (60mks)
Answer question 16 and any other three questions from this section in the spaces provided.
-
- With the aid of a flow chart describe a loop control structure as used in programming. (4mks)
- Study the following pseudocode and answer the questions that follow;
- Start
- Get value 1 and value 2
- If value 1 >value 2 then
- Maxmum = value 1
- Else if value 1<value v Then
- Maximu= value 2
- Else go to 9
- Display maximum
- Stop
- State the purpose of the pseudocode (1mk)
- Draw a flowchart equivalent to the pseudocode. (6mks)
- Distinguish between a source program and a compiler as used in computer programming. (4mks)
-
- Explain the term search enquire as used in the;
- Internet (2mks)
- Peter intends to download a movie from the internet. State any three factors that determine the total time taken to complete the download. (3mks)
- Wakulim aonline is an organization that runs a web based system for assisting farmers to obtain market for their farm produce;
State four technological reasons that may causes a farmer not to access the organizations system. (4mks) - Explain a situation when each of the following Desktop publishing program features may be used when creating a publication;
- Cropping (2mks)
- Transparency. (2mks)
- List two areas where infrared waves are used in data communication. (2mks)
- Explain the term search enquire as used in the;
-
- State four activates of the planning stage of system development. (4mks)
- Explain a circumstance when each of the following feasibility studies are carried out during system development;
- Technical (2mks)
- Economic (2mks)
- Schedule (2mks)
- Table 1 and table 2 are related tables in a database. Use them to answer the questions that follows.
Table 1
Table 2Dept
Dept Name
001
002
003
Computer
Aviation
Engineering
Dept
Students Registration
students
ID
No
Name
002
003
002
St1
St2
St3
Alex Toro
Naomi Komi
Peter kengo
- Identify the appropriate primary key for each table. (1mks)
- Explain two benefits of enforcing referential integrity in a database. (4mks)
-
- Describe the following validation checks as used in data processing;
- Preserve check. (2mks)
- Data type check. (2mks)
Check digit. (2mks)
- Write each of the following abbreviations in full;
- ACB. (1mk)
- EBCD (1mk)
- ASCLL (1mk)
- Using 10 – bits binavy number system, performs the following decimal operation using two’s compliment. (6mks)
- 129 (10)
- 128 (10)
- Describe the following validation checks as used in data processing;
-
- The figure shows a network design. Use it to answer the questions that follow.
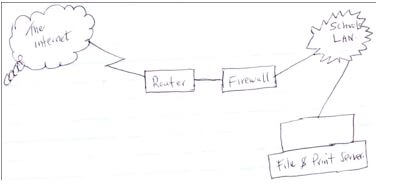
- Explain the functions of each of the following in the network.
Router (2mks)
Firewall (2mks)
File server (2mks) - State two categories of software that must be installed in a computer so that users can use it to access the internet. (2mks)
- Explain the functions of each of the following in the network.
- State four ways in which computer may be used to manage data in a research environment. (4mks)
- Some computer companies have opted to use the internet to provide shared processing research and online application services to users.
State three advantages that this approach will have on their customers. (3mks)
- The figure shows a network design. Use it to answer the questions that follow.
Download Computer Studies Paper 1 Questions - Form 4 Term 2 Opener Exams 2023.
Tap Here to Download for 50/-
Get on WhatsApp for 50/-
Why download?
- ✔ To read offline at any time.
- ✔ To Print at your convenience
- ✔ Share Easily with Friends / Students