INSTRUCTIONS TO CANDIDATES
- This paper consists of TWO sections A and B
- Answer all questions in section A.
- Answer question 16 (Compulsory) and any other THREE questions in section B.
- All answers should be written in the spaces provided in the question paper
SECTION A (40 MARKS)
Answer all questions from this section in the spaces provided
- List the components of a computer system hardware. (2 Marks)
…………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Describe the term key to storage systems (1 Mark)
…………………………………………………………………………………………………………………………………………………………………………………………………………………………… - One classification of software is system software
-
- What is meant by system software (1 Mark)
…………………………………………………………………………………………………………………………………………………………………………………..……………………………………… - Give one example of system software. (1 Mark)
……………………………………………………………………………………………………………………………………………………………..……………………….……………………………………
- What is meant by system software (1 Mark)
-
- Name one other software classification (1 Mark)
…………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Give one example of this type of software (1 Mark)
…………………………………………………………………………………………………………………………………………………………………………………………………………………………
- Name one other software classification (1 Mark)
-
-
- What do you understand by the term database management system? (DBMS)? (1 Mark)
………………………………………………………………………………………………………………………………………………………………………………………………………………………………. - Define the following terms as used in a database. (2 Marks)
- Primary Key
……………………………………………………………………………………………………………… - Record
………………………………………………………………………………………………………………
- Primary Key
- What do you understand by the term database management system? (DBMS)? (1 Mark)
- Differentiate between COMports and LPT ports (2 Marks)
…………………………………………………………………………………………………………………………………………………………………………………………………………………………… - List three factors to consider when deciding on the choice of electronic data processing method (3 Marks)
……………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Ventilation is an important practice in the computer lab because it enhances proper circulation of air.
Outline three ways in which air is regulated in the computer room. (3 Marks)
……………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………… - What do the following control measures against computer crime involve? (4 Marks)
- Audit trail
………………………………………………………………………………………………………………. - Data encryption
……………………………………………………………………………………………………………….. - Log files
…………………………………………………………………………………………………………… - Passwords
……………………………………………………………………………………………………………
- Audit trail
- Highlight the use of find and replace features in word processors. (2 Marks)
……………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Explain why two’s complement is preferred to one’s complement in computing. (1 mark)
……………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Computers have evolved through a number of generations. List any three characteristics of the first generation of computers. (3 marks)
…………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………… - List four formatting techniques used in Ms excel (2 Marks)
………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………. - List four examples of flat panel displays. (2 Marks)
……………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Explain the following terms as used in the word processing. (4 Marks)
- Indenting
………………………………………………………………………………………………………………. - Alignment
………………………………………………………………………………………………………………. - Footnote
………………………………………………………………………………………………………………. - Endnote
………………………………………………………………………………………………………………..
- Indenting
- Describe the role of an operating system in
- Memory management
……………………………………………………………………………………………………………….. - Job scheduling
………………………………………………………………………………………………………………… - Error handling
…………………………………………………………………………………………………………….. - Resource control
………………………………………………………………………………………………………………..
SECTION B (60 MARKS)
- Memory management
-
- State the three basic types of program control structures. (3 Marks)
…………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………….. - Draw a flowchart which will simulate the processing of student’s report. The simulation should be such that the user repeatedly inputs marks per subject for six subjects using a looping control structure. The computer processes the total marks and mean score of the student.
NOTE:- It is assumed that the student does six subjects
- The output required are: Average score and total marks
- Differentiate between analogue and digital data. (2 Marks)
……………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Outline three advantages of using computers for data processing over other types of office and business equipment.
………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………
- State the three basic types of program control structures. (3 Marks)
-
- Convert the following numbers to their decimal equivalent. (6 Marks)
- 11.0112
……………………………………………………………………………………………………………………………………………………………………………………………………………………………… - 12.158
……………………………………………………………………………………………………………………………………………………………………………………………………………………………… - A3.3/6
………………………………………………………………………………………………………………………………………………………………………………………………………………………………
- 11.0112
- Outline four ways in which data integrity may be maintained. (4 Marks)
………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………. - Explain four advantages of using questionnaires as a fact finding tool. (4 Marks)
……………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………… - What is the role of a recycle bin? (1 Mark)
………………………………………………………………………………………………………………
- Convert the following numbers to their decimal equivalent. (6 Marks)
-
- Masai teacher’s college has decided to automate its library for effective services to the students. Identify four methods they are likely to use to gather information during system development. (4 Marks)
………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………. - What do the following terms mean in relation to internet? (4 Marks)
- Downloading
……………………………………………………………………………………………………………….. - Hyperlink
……………………………………………………………………………………………………………….. - Web browsers
………………………………………………………………………………………………………………. - Internet service providers
………………………………………………………………………………………………………………
- Downloading
- Differentiate between sorting and filtering as used in electronic spreadsheet program (2 Marks)
…………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………….... - What do the following terms mean
- Spam mail
……………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Disk
……………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Onboard moderm
………………………………………………………………………………………………………………………………………………………………………………………………………………………………
- Spam mail
- What does the term WIMP mean as used in computing?
……………………………………………………………………………………………………………………………………………………………………………………………………………………………..
- Masai teacher’s college has decided to automate its library for effective services to the students. Identify four methods they are likely to use to gather information during system development. (4 Marks)
-
- Define a database model (1Mark)
……………………………………………………………………………………………………………………………………………………………………………………………………………………………… - List four advantages of using database systems (2marks)
……………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………… - In a database system, data integrity ensures the correctness and completeness of the data in the database. Differentiate the following types of integrity constraints:
- Validity integrity (1mark)
……………………………………………………………………………………………………………… - Entity integrity (1mark)
………………………………………………………………………………………………………………. - Referential integrity (1mark)
………………………………………………………………………………………………………………
- Validity integrity (1mark)
- Briefly describe the three database models (3 Marks)
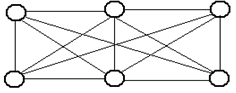
……………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Using diagrams describe the following three types of relationships. (3Marks)
- One – to – one
- One – to – many
- Many – to – many
- File organization refers to the arrangement of records on secondary storage. Briefly describe the following file organization methods. (3 Marks)
- Serial
………………………………………………………………………………………………………….. - Sequential
…………………………………………………………………………………………………………. - Random
…………………………………………………………………………………………………………..
- Serial
- Define a database model (1Mark)
-
- Your School has decided to replace its library control system. The current system was implemented ten years ago but has restricted reporting facilities and has a text – based interface. The school intends to replace the old system with a new computerized system, and is now considering both ‘parallel running ‘ and ‘direct changeover’
- Briefly explain the terms parallel running and direct change over as used in system implementation. (2 Marks)
………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Give two disadvantages of direct changeover overparallel running (1 Marks)
……………………………………………………………………………………………………………………………………………………………………………………………………………………………….. - Identify two main risks of direct changeover during system implementation (2 Marks)
……………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Mention any two advantages of running both the manual system and the computerized system simultaneously (2 Marks)
………………………………………………………………………………………………………………………………………………………………………………………………….…………………………..
- What is a website? (2 marks)
……………………………………………………………………………………………………………………………………………………………………………………………………………………………… - Name three facilities that are needed to connect to the internet. (3 Marks)
………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………
- Briefly explain the terms parallel running and direct change over as used in system implementation. (2 Marks)
- State three ways students can benefit by having internet in a school (3 Marks)
………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………………
- Your School has decided to replace its library control system. The current system was implemented ten years ago but has restricted reporting facilities and has a text – based interface. The school intends to replace the old system with a new computerized system, and is now considering both ‘parallel running ‘ and ‘direct changeover’

MARKING SCHEME
-
- Input – accepts in data and converts it into computer understandable form
- Processor – manipulates data into information
- Storage – holds data, instruction and information in the computer.
- Output – gives the results of processing to the user
- These are microcomputers - based systems that take in data from the VRU (Keyboard, mouse and monitor) and store it in diskettes
-
- System software refers to the programs that control the performance of the computer.
- Utility programs, O/S, compilers and interpreters
- Application software
- Word processors, spreadsheet, RBMS
-
- DBMS – collection of data programs (software) that help one retrieve data and perform operations on it. It involves creating, modifying, deleting and adding data files and using this data to generate reports.
-
- Primary key – an attribute of a relation that uniquely identifies all the other attributes
- Record – collection of related fields (data items)
-
- Com – ports are used for serial cables
- LPT ports are used for parallel cables connection
-
- Suitability of accumulating data
- Response time
- Cost of initial installation and operations
- Ease of development and subsequent maintenance
-
- Avoid overcrowding of either machines or users in the room
- Ensuring that the room has enough ventilation points like windows
- Installing air conditioners
-
- Audit trail – Careful study of an information system by experts to establish all weaknesses in a system that could lead to security threat.
- Data encryption - Combination of letters and characters that deter unauthorized access
- Log files – special files that keep a record of events on the use of computer resources
- Password – combination of characters that deter unauthorized user from accessing data.
- It is used to look for specified words in a document and replacing them with alternative.
- There is only one way of representing a zero unlike in ones compliment
-
- Large in physical size
- Used thermionic valves
- Consumed a lot of power
- Constant breakdown
- Low memory and processing speed
- Cost was high
-
- Change text colour
- Change font size
- Change font style
- Text alignment
-
- Gas plasma
- Electro luminiscent
- Thin film transistors
- Liquid crystal display
-
- Identing – move text away from the left margin
- Alignment – placing text on page relative to right, left or centre of the page
- Footnote – additional piece of information printed at bottom of page
- End note – notes collected under separate heading at end of chapter in a document
-
- Load application programs from external storage in to main memory. Also note the part of main memory in use and free
- Prepares jobs for continuous execution determining the first task to be done and last one.
- Reports errors that occur during execution
- Control use computer hardware by system software and application programs.
SECTION B
-
- Sequence
Selection
Iteration 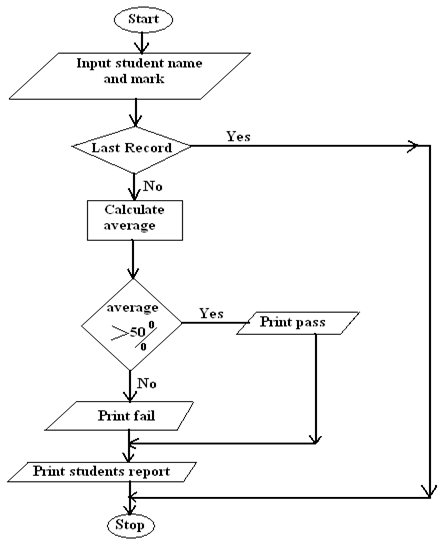
- Analog is continuous in nature. While digital is discrete in form
-
- Computers are fast
- Produce more accurate results
- Produce neat work
- Are more efficient
- Sequence
-
-
- (20x1) + (21x1) + (2-1 x 1) + (2-3 x 1)
- 2 + 1 + 0+0.25 + 0.125
= 3.37510
(1x81) + (2x80) + (1x8-1) + (5x8-2)
8 + 2 +1/8 +5/64
= 10 13/6410 or 10.20310
(10x161) + (3x160) + (3x16-1)
160 + 3 + 3/16
= 163 3/1610
-
- Back up data
- Control data access
- Design interface that minimize invalid data entry
- Use data capture service
-
- Can reach many respondents
- Give many responses
- Saves time
- Minimjze biasness
- Contain the deleted files
-
-
-
- Questionnaires
- Interviews
- Observations
- Note taking
- Study available documents
- Tape recording
-
- Process of transferring information from remote computer to local storage.
- Text or picture in an electronic document
- Applications that enable a person to access the internet.
- Companies that offer internet services to end users.
- Sort is to arrange data in a predefined order either ascending or descending. While filtering is a quick and efficient method of finding and working with a subject within a list.
-
- A mail sent to many people indiscriminately.
- Flat circular plate covered in a magnetic which is able to store data on concentric tracks.
- Modem fixed on mother board
- Windows icons mouse and pointing devices
-
-
- The arrangement of data in a file which determine the access method.
-
- Control of data redundancy
- Maintain data consistency
- Sharing of data
- Improved date integrity
- Economy of scale
- Improved security
-
- Ensure that the data fields contain the correct data type
- Primary key cannot have empty values.
- A foreign key can only have the values of the relevant primary key.
-
- Hierarchical model – Records in the database can be related in one parent only but can have more child records.
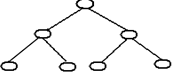
- Network – any record can be related with any other record.
- Relational model – all data is logically structured within tables.
- Hierarchical model – Records in the database can be related in one parent only but can have more child records.
- One to one – for any member of A there is only one member of B and for any member in B there is one member of A.

One to many – for a single member of A, there may be multiple associations with it B but for any B member there is only one member of A associated with it.
Many to many – for member in A there may be more members of B and for any member in B there may be many members of A
-
- Serial – records are placed on the disk with no particular order.
- Sequential – records are placed on disk according to a specific field
- Random – A hash function calculates the address of the page in which the record is to be stored based on one or more of the fields.
-
-
-
- Parallel running – both old and new systems run in parallel to each other
- Direct changeover – complete replacement of the old system with the new system in one move.
-
- It may be inconveniencing incase the new system fails/face problem.
- The users may not have gained enough confidence to run the new system.
-
- Incase of system failure
- If testing was not thoroughly done.
- Requires training on new programs
- Requires new hardware and software (costs)
-
- Promotes confidence as a result of same input and output
- Training is done to enable familiarization
- Reliable in terms of testing
-
- Collection /group of related WebPages belonging to an organization or individual
-
- Internet software
- Telecommunication facilities
- Modem
- Internet service provider
- TCP/IP protocol
-
- Exchange programs with students in other schools
- E-learning
- Research widely
-
Download Computer Studies Paper 1 Kenya High Post Mock Exams 2020 - Questions and Answers.
Tap Here to Download for 50/-
Get on WhatsApp for 50/-
Why download?
- ✔ To read offline at any time.
- ✔ To Print at your convenience
- ✔ Share Easily with Friends / Students