- Differentiate between cold booting and warm booting in computing. (2mks)
Cold booting – is to start up a computer that is turned off.
Warm booting - to restart a computer and reload the operating system - Define parallel processing. (1mk)
Parallel processing is the simultaneous use of more than one CPU to execute a program.Processing of program instructions by dividing them among multiple processors with the objective of running a program in less time. Parallel processing makes a program run faster because there are more CPUs running it.
- Mention any TWO reasons why command-based operating systems are not common in today’s business computer systems. (2mks)
-It is difficult to remember commands.
-Cannot process graphics e.g. pictures, drawings or videos.
-Hardly makes use of emerging hardware and software technologies. - Explain any THREE functions of an operating system with respect to memory management. (3mks)
-Keeping track of which parts of memory are currently being used and by whom.
-Deciding which processes to load when memory space becomes available.
-Deciding how much memory is to be allocated to a process.
-Allocating memory space as needed.
-De-allocating memory space as needed.
- Mention any TWO reasons why command-based operating systems are not common in today’s business computer systems. (2mks)
- Differentiate between partitioning and formatting as used in disk management (2mks)
-Partitioning is dividing a hard drive into logical portions or sections for specific arrangement of data. For example, one partition for installing operating system and another for users data.It logically groups a part of memory in the disk to create address table for files to be stored.
-Formatting is preparing a disk in order for it to accept data storage, by arranging its tracks and sectors. - Name the type of scanner used to capture data from the following document format below. (1mk)
-Magnetic Ink Character Reader/Recognition
- Computer output can now be in form of spoken words in digitized speech. An example of such application is spell learning devices for children. State ONE advantage of speech output. (1mk)
-No reading is necessary, useful for short messages.
-Useful in situations where you can’t look or where you are busy.
-Fast, natural output.
-People are fond of ‘Computer talk’ - Mention any TWO features that are considered before buying a main memory module. (2mks)
-Type of memory package e.g. DDR, DDR II
-Whether there is empty memory slot in the computer.
-Compatibility with other installed modules.
-Capacity of the module - how much data it can hold. - A technician recommended a computer in the principal’s office needs upgrading of the CPU. State any TWO reasons that may have necessitated the upgrading of the CPU. (2mks)
-The CPU overheating regularly
-Applications loading slower than expected.
-Graphics, video or data transfer speeds become sluggish. - State TWO reasons why secondary storage is preferred to main memory in data storage. (2mks)
-High data storage capacity: It is often necessary to store many millions, sometimes billions and even trillions of bytes of data in a computer. Unfortunately, the storage capacity of the primary storage is not sufficient to store large volumes of data which needs to be handled by most data processing centers/systems.
-Non - volatility: Data in it is lost when power is turned off or interrupted. However, computer systems need to store data on a permanent basis for several days, months or even several years. - State ONE advantage of relational database model over flat files. (1mk)
-No multiple record changes needed
-More efficient storage
-Simple to delete or modify details.
-All records in other tables having a link to that entry will show the change.
-Avoids data duplication
-Avoids inconsistent records
-Data can be added and removed easily
-Easier to maintain security. - State TWO uses of primary keys in a database. (2mks)
-It is used to prevent double data entries.
-Used to link records that are related records.
-Used to speed up searching
-Used to perform indexing to ensure uniqueness of datarecords. - A database requires data to be defined by assigning data types to fields for purposes of consistent storage. Describe any FOUR data types that can be allowed in Ms Access. (4mks)
-AutoNumber - Numbers that are automatically generated for each record.
-Currency - Monetary values.
-Date/Time - Dates and times.
-Hyperlink - Hyperlinks, such as e-mail addresses.
-Memo - Long blocks of text and text that use text formatting. A typical use of a Memo field would be a detailed product description.Memo is used for larger amounts of text. Stores up to 65,536 characters. Note: You cannot sort a memo field. However, they are searchable
-Number - Numeric values, such as distances. Note that there is a separate data type for currency.
-OLE Object - OLE objects, such as Word documents.
-Text - Short, alphanumeric values, such as a last name or a street address.255 characters maximum
-Yes/No - Boolean values.
-Byte- Allows whole numbers from 0 to 255
-Attachment - Files, such as digital photos. Multiple files can be attached per record. This data type is not available in earlier versions of Access. - Define the term macro as used in databases (1mk)
A macro is a tool that allows you to automate tasks and add functionality to your forms, reports, and controls.
- State ONE advantage of relational database model over flat files. (1mk)
- State any ONE reason why USB interface cables are widely used in computing devices. (1mk)
-Higher Speed
USB runs at up to 12Mbit/second; that's 12,000,000 bps (bits per second). It is not subject to data loss due to overflows and missed interrupts. USB has none of those problems - speed is reliable and high.
-Multiple Devices
A USB port can run many devices at once, up to 128 in total. To add more devices to a single port, a low cost hub (splitter) can be used. Hubs are often built into monitors. The great advantage is that you no longer have to worry about having enough ports for new peripherals or use ports for purposes for which they weren't intended (e.g. external tape drives on parallel ports
-Self-Powered
USB provides power to the peripheral you connect, so there is no need for an external main for most products.
Truly Plug & Play
USB devices configure themselves; your PC will automatically detect the new device and install the software for it.
-Hot-Swappable
USB devices can also be hot-swapped - i.e. connected or removed while the PC is switched on. - A company is considering replacing some of its software, including its word processing package, and to acquire an integrated software package. State TWO advantages for the company in using intergrated software rather than separate packages. (2mks)
-It allows WP, database and spreadsheet tasks to be carried out using the same program i.e. layouts and instructions will be similar which can make it easier to learn and use all applications. (Packages will share a common HCI (Human Computer Interface).
-Can be cheaper than buying the software packages individually.
-Mail merge can be carried out within the package.
-Transfer data easily between packages e.g. copying a chart from spreadsheet into a word processing document.
-More than one package can be open at the same time.
-Dynamic linkage is possible. - State TWO types of DTP software. (2mks)
-Layout based
-Graphics based - List FOUR page formatting features in DTP (2mks)
-Column guides
-Page numbers
-Margin guides
-Page breaks
-Column breaks
-Headers and footers
- State TWO types of DTP software. (2mks)
- Explain the meaning of “what if analysis” in spreadsheets. (2mks)
It is a scenario where spreadsheets take sets of input values and determine possible results, used to forecast future trends and possibilities by changing values to see the effect.
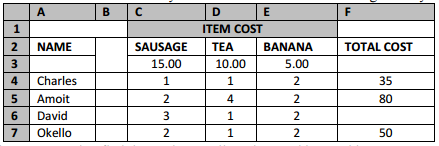
- The table below shows items consumed by some students for breakfast in a given day.
- Using an expression, find the total expenditure incurred by David. (2mks)
=SUM(C3*C$2)+(D3*D$2)+E3*E$2
OR
=SUM(C3*15)+(D3*10)+E3*5 - State what you would obtain from the expression = CountIF (F4:F7, “>45”) (1mk)
It returns the number of values greater than 45, within the range given, which is 4.
- Using an expression, find the total expenditure incurred by David. (2mks)
- Explain the meaning of “what if analysis” in spreadsheets. (2mks)
- Define the following terms as used in relation to operating systems (2mks)
- Folder
A container of files, which helps in grouping or organizing files. Also known as directory.
- Drive
A drive is a medium that is capable of storing and reading information that is not easily removed like a disk.
SECTION B (60 MARKS)
ANSWER QUESTION 16 AND ANY OTHER THREE QUESTIONS FROM THIS SECTION
- Folder
- State any THREE advantages of using Object Oriented programming for writing programs (3mks)
-Improved software-development productivity: Object-oriented programming is modular, as it provides separation of duties in object-based program development.
-Improved software maintainability: For the reasons mentioned above, object-oriented software is also easier to maintain. Since the design is modular, part of the system can be updated in case of issues without a need to make large-scale changes.
-Object-oriented programming languages come with rich libraries of objects, and code developed during projects is also reusable in future projects.
-Lower cost of development since some objects can be reused in software.
-Faster development of software and lower cost of development allows more time and resources to be used in the verification of the software. - In a computer contest with 40 entries, three papers are tested and the final marks awarded according to the average of the papers. The final marks are then ranked to get position 1, 2 and 3 who are awarded trophy, cash and scholarship, trophy and cash, and cash respectively.
Write a program pseudocode and flowchart that will prompt for the name, school and marks for each paper then compute the final marks and rank and display the students name, school, final marks position and award.- Pseudocode (5mks)
Start
Position=o
Rank=0
N=0
For students (n) = 1 to 40 do
Papers =1
Total = 0
Print “please enter the students Name and School”
Input name, school
While papers<=3 do
Print “please enter marks for paper”, papers
Input marks
Total= total + marks
Average = total/papers
Papers=papers + 1
End while
If average >= 80 then
Grade = “A”
Position = 1
Award = trophy, cash and scholarship
Else
If average >= 60 then
Grade = “B”
Position = 2
Award = “trophy and cash “
Else
If average >= 40 then
Grade = “C”
Position = 3
Award = “cash”
Else
If average >= 20 then
Grade = “D”
Position = 4
Award = “no award”
Else
Award = “no award”
End if
End if
End if
End if
End for - Flowchart (7mks)
- Pseudocode (5mks)
- State any THREE advantages of using Object Oriented programming for writing programs (3mks)
- With the aid of a well labeled diagram, describe control and feedback model in a system (4mks)
-Feedback and Control
A system with feedback and control components is a self-monitoring and a self-regulating system.
-Feedback is data about the performance of a system. For example, data about sales performance is feedback to a sales manager.
-Control involves monitoring and evaluating feedback to determine whether a system is moving toward the achievement of its goal. The control function then makes necessary adjustments to a system’s input and processing components to ensure that it produces proper output. For example, a sales manager exercises control when he or she reassigns salespersons to new sales territories after evaluating feedback about their sales performance. - Distinguish between the following terms as used in system development. (4mks)
- Hard system and soft system
-Soft system have got no clearly defined goals and objectives hence their performance cannot be precisely measured. For example, sales tracking system where sales performance depend on human factors such the prevailing conditions (availability of money, customers, products) and human preferences.
-Hard systems are systems whose goals and objectives are clearly defined and the outcomes from the processes are predictable. For example, in a stock control system, it is possible to know exactly the stock levels, the reorder and profits can be accurately predicted if all the stock is sold.
- Operational feasibility and technical feasibility.
-Operational Feasibility - is a study done to determine whether the users would be able to operate the new system with minimal retraining. The new system should fit well into the existing operational structure of the organization.
-Technical Feasibility - This is a study done to assess whether the work for the project can be done with the present equipment, current procedures, existing software, technology and available personnel. If new technology is needed, what alternatives will be needed in the present structure and work ethos?.
- Hard system and soft system
- State THREE ways in which organizations manage system entropy. (3mks)
-Training of knowledge workers on changing attributes or parameters of the workplace especially software and hardware technologies. Workers can be trained
-Outsourcing expertise to improveon competitive edge practices in information systems management.
-Utilize capacity for feedback— that is, information about the output that can be used to control the system. Organizations can correct errors and even change themselves because of this characteristic. Organizations have the potential to use feedback to become self-correcting systems, but they do not always realize this potential.
-For system to survive it must maintain favorable balance of input or output transactions with the environment or it will run down. For example, adjusting to government directives or changing policies, and user requirements. - Explain any TWO reasons for system maintenance. (1mk)
-To improve the performance of the system
-To make modifications to the system or to an individual component to alter its attributes to suite the needs of the organization - Briefly explain THREE ways in which computers can be used in motor vehicle manufacturing companies. (3mks)
-Designing motor vehicles models using CAD& CAM applications.
-Motor vehicle assembling using robot to fix together the parts of the vehicle
-Motor vehicle testing and collision analysis using simulators.
-Industry wet paint spraying.
- With the aid of a well labeled diagram, describe control and feedback model in a system (4mks)
- Distinguish between the following terms as used in data communication. (4mks)
i. Guided transmission and unguided transmission-Guided transmission medium is a transmission medium that transmits data to its destination using a physical medium such as cables while unguided transmission media is one that transmits data though free space. There is no physical connection between the communicating devices.
ii. Multiplexing and demultiplexing-Multiplexing Is the process of sending multiple data signals over a single medium along a communication channel. While demultiplexing is the process of separating the multiplexed signals at the receiving end of a channel back to the number of transmmission chansmission channels multiplexed.
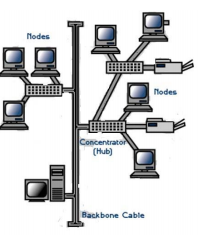
- Below is a diagram of a network topology.
i. Name the above topology. (1mk)-Tree topology
ii. State ONE advantages and ONE disadvantage of using the topology named above. (2mks)Advantages
-It allows for Point-to-point wiring for individual segments.
-It is supported by several hardware and software vendors.
Disadvantages
-Overall length of each segment is limited by the type of cabling used.
-If the backbone line breaks, the entire segment goes down.
-It is more difficult to configure and wire than other topologies. - State TWO ways in which users in an organization can be a security threat to data in an information system. (2mks)
-Through accidental access to files they are not supposed to access
-By using confidential data for their own personal gain
-Through intentional access to unauthorized data - Define cyber terrorism. (1mk)
The use of a computer as a tool and a vehicle to intimidate and pressurize other
- State TWO ways in which users in an organization can be a security threat to data in an information system. (2mks)
- A school intends to set-up an e-mail. List FOUR activities likely to be provided by the e-mail facility. (2mks)
-Composing mails
-Attaching files
-Sending and receiving mails
-Cloud services e.g. gmail drive, google docs
-Online discussions
-Sharing of messages (e.g. google groups)
-Mail merging - Define the following terms as used in the internet. (2mks)
- Internet blog
An online diary that contains recent news and personal opinions on some specific topics. These are personal websites that contain information that is accessible to the public with conditions
- Webportals
This is a website that provides specialized services such as email, searching, news updates, weather, financial updates and links to selected websites
- Internet blog
- Kenya publishing and printing company wishes to employ an ICT professional to assist in making publications .State the suitable ICT professional the firm could employ. (1mk)
-Graphic designer/Typesetter
- Distinguish between the following terms as used in data communication. (4mks)
- List and explain the THREE types of errors that can occur during data collection stage of data processing cycle. (3mks)
-Transposition error: Errors occurring as a result of interchanging the position of characters during data entry
-Transcription error: Errors as a result of wrong data entry
-Algorithm errors – errors that occur from the wrong use of an algorithm or procedure in solving a given problem in a computer. - Distinguish between master file and transaction file. (2mks)
-Master file stores permanent or semi-permanent data
-Transaction file:Used to update semi-permanent data on a master file - Define real time processing. (1mk)
Data is processed immediately it is received and the result is automatically used to update the current situation
- Explain a situation where the batch processing would be appropriate. (1 mark)
Appropriate where information is not required immediately since data is accumulated over a specified period of time and the processed as a group
- List and explain the THREE types of errors that can occur during data collection stage of data processing cycle. (3mks)
- Using twos complement, perform the following operation and give your answer in decimal notation
7778 - 2510 (4 marks)Convert to binary 7778=1111111112
2510=110012
Ones complement
0000110012=1111001102
Twos complement
1111001102+1=1111001112
1111111112+1111001112=11111001102 (ignore overflow)
=1111001102 to hexadecimal=1E616
To decimal (1*162) +(14*161) +(6*160)= 48610 - Solve AC16+1012 = X2 (2 marks)
A=10102
C=11002
AC16=101011002
101011002+1012=101100012 - Convert binary number 11010110.10012 into octal number. (2mks)
001/010/10=4368
- State any TWO negative effects of introducing robots in a manufacturing plant (2mks)
-Wide use of robots probably increases the unemployment rate. with the enrollment of robots and improvement of working efficiency, factories need not so many labors that many people are fired.
-Robots work by following some designated instructors. in some urgent and dangerous situation, robots cannot adjust automatically to fit the change and lead to serious consequence.
-The widespread use of robots decrease the independence of human on machines, weaken the creativity ability of human indirectly. - State THREE advantages of using computers. (3mks)
-Computers makes it possible to receive, supply and process large volumes of data at very high speed.
-More information sources
-More opportunities for cooperation and networking
-Increased access to the information in the resource center.
-Increased efficiency
-More services
-Computer greatly improves the speed of data input, output, processing, and transmission.
-Computer ensures consistent and error free processing of data. - Name THREE types of special purpose memories used in a computer. (3mks)
-Buffers
-Registers
-Cache memory - Explain the purpose of the system clock. (2mks)
Ensure the correct synchronization of the fetch and execute cycle
- In word processing, differentiate between text wrap and word wrap. (2mks)
-Text wrap is the process of fitting text around an image with a narrow margin. Depending on the size and placement of the image, the text may wrap around the left, right, or both sides of the image.
-Word wrap- As text approaches the end of a line (the margin), if a word won't fit it wraps or continues at the beginning of the following line. - List any THREE types of section breaks used in word. (3mks)
-Next page
-continuous
-Even page
-Odd page
- In word processing, differentiate between text wrap and word wrap. (2mks)
- State any TWO negative effects of introducing robots in a manufacturing plant (2mks)
Download MOKASA Joint Evaluation Examination Computer Studies 1 2016- Pre MOCK.
Tap Here to Download for 50/-
Get on WhatsApp for 50/-
Why download?
- ✔ To read offline at any time.
- ✔ To Print at your convenience
- ✔ Share Easily with Friends / Students