INSTRUCTIONS TO CANDIDATES:
- Write your name and index number in the spaces provided above.
- Write the date of examination and sign in the spaces provided.
- This paper consists of two sections.
- Answer all the questions in section A.
- Answer question 16 (compulsory) and any other three questions from section B.
- All answers must be written in the spaces provided in this question paper.
FOR EXAMINER’S USE ONLY
|
SECTION |
QUESTION |
MAXIMUM SCORE |
ACTUAL SCORE |
|
A |
1 – 15 |
40 |
|
|
B |
16 |
15 |
|
|
15 |
|||
|
15 |
|||
|
15 |
|||
|
TOTAL SCORE |

QUESTIONS
SECTION A (40 MARKS)
ANSWER ALL THE QUESTIONS FROM THIS SECTION IN THE SPACES PROVIDED
- One of the functions of an operating system is to control computer resources. State three resources under operating system control (3 marks)
-
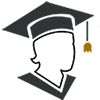
- The figure below shows the relationship between tables in a database.
Identify two primary keys and two foreign keys used in the relationships (2 marks) - Distinguish between bound and unbound controls as used in database forms (2 marks)
- The figure below shows the relationship between tables in a database.
- Explain why an impact printer is suitable for printing multiple copies (2 marks)
- State any four examples of document readers (2 marks)
-
- Define the term simulation (1 mark)
- List two educational areas where simulation programs can be used (1 mark)
- Explain two ways of protecting data and information against unauthorized access (2 marks)
- Explain two characteristics of good information (2 marks)
- Explain three types of errors that are likely to exist in a program (3 marks)
- State two roles of a network admistrator (2 marks)
- State three negative impacts of information communication technology on the environment (3 marks)
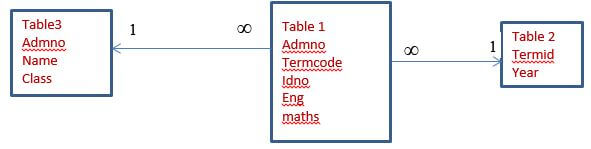
- Study the follow flowchart then answer the questions that flow.
- Identify the type of flowchart represented by the flowchart in figure (1 mark)
- Name the flowchart symbols labeled A, B,C and D in the flowchart. (2 marks)
- Mary a computer student noticed that every time a person enters the computer lab, the computer screen flickered. Identify three reasons why the monitor might be flickering (3marks)
-
- state the importance of column breaks as used in a word processor (1 mark)
- List any two line spacing specifications used in Ms- Word (1 mark)
- The first column in the table below contains the formula stored in cell C10 of a spreadsheet. Enter the formula as they would appear when copied to cell F15 of the same spreadsheet (2 marks)
FORMULA IN C10
FORMULA IN F15
=A5*B5
=4*B$6
-
- Differentiate between an analog and digital data signal (2 marks)
- The government of Kenya is in the process of laying out fibre optic cables throughout the country. State three advantages of fibre optic cables (3 marks)
SECTION B( 60 MARKS)
ANSWER QUESTION 16 AND ANY OTHER THREE QUESTIONS FROM THIS SECTION
-
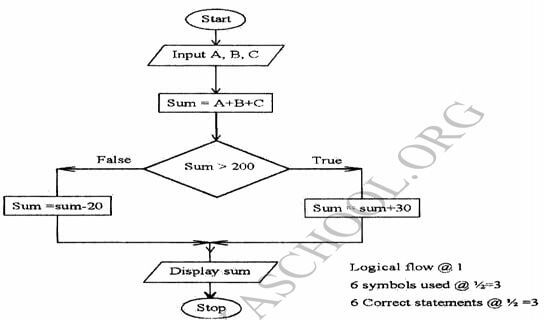
- Draw a program flowchart that would accept and their sum. If the sum is greater than 200, it adds 30 to the sum, otherwise subtracts 20 from the sum. The program should then display the results (7 marks)
- Study the pseudo code below and determine its output (3 marks)
STEP 1: T=0
M=0
K=1
STEP 2 M=M+T
T=T+5
K=K+1
STEP 3 REPEAT STEP 2 WHILE K<3
WRITE M, T
EXIT -
- List two benefits of using interviews as a method of fact finding (2 marks)
- Explain three types of system change over strategies (3 marks)
-
- state three functions of a database management system (DBMS) (3 marks)
- if a database was to be created for a list, Tables, Forms, Queries and Reports are likely to be used. State the purpose of each of the objects (4 marks)
- The information below is maintained by Jessica Fruit store. Study it and answer the questions that follow:
Write down the query statements you can use to list the following;Product number
Product name
Qty in stock (kg)
Value per unit (ksh)
001
Peach
1000
200
002
Oranges
1200
200
003
Mangoes
1300
100
- Product names starting with letter P. (2 marks)
- Value per unit below 200. (2 marks)
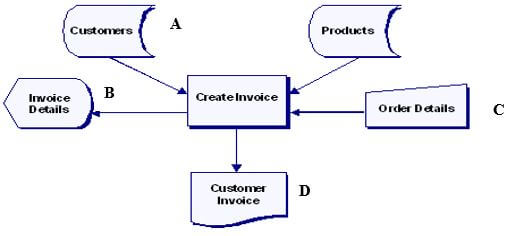
- The following is a spreadsheet relating to a farmer (2 marks)
A function = IF (B2<200, “Not Viable”, IF (B2>300, “Moderate”, IF (B2>1000, “Viable”))). Give the appropriate result returned in cells C2, C3, C4 and C5
Name four data types used in spreadsheets. (2 Marks)
-
- Explain the use of the following commands found in the spell check dialog box in reference to word processing (3 Marks)
- Change
- Ignore once
- Add
- State four font styles supported by Ms. Word (2marks)
- Work out the following binary arithmetic (2marks)
- 11101.00112 + 101.0112
- 101001.101012-110.011012
- Using twos complement, perform the following calculation. (4marks)
2310 - 4110 - Convert 13.12510 to decimal. (2marks)
- A particular computer stores numbers in a single 8-bit word. How would it represent 0.312510? (2 marks)
- Explain the use of the following commands found in the spell check dialog box in reference to word processing (3 Marks)
-
- Explain each of the following type of operating systems (4marks)
- Distributed
- Multi-user.
- List any two types of embedded operating systems used in modern cell phones (2marks)
- Most operating systems provide a file system. Mention any TWO file systems used in windows environment. (2 marks)
- Define the term interactive data processing. (1mark)
- Explain why input screens are better data entry designs than entering data directly a table. (2 marks)
- State two likely causes of data and program loss in a computer system? (2 marks)
- Explain the meaning of the following terms as used in data security (2marks)
- Fraud
- Alteration
- Explain each of the following type of operating systems (4marks)
-
- The figure below shows an extract of an e-mail application.
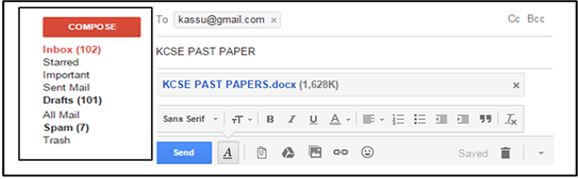
State what is meant by the following (3 marks)- Trash
- Spam
- Inbox
- Explain the following interactive sensory equipment used in virtual reality (2marks)
- Head gear
- Body suit
- Most computerized security systems make use of Biometric analysis, name three physical features of human beings that can be considered in this analysis (3marks)
-
- Define the term networking topology (1mark)
- Distinguish between logical and physical network topologies (2marks)
- Explain the functions of the following network devices (4marks)
- Network interface card (NIC)
- Gateway
- Bridge
- Repeater
- The figure below shows an extract of an e-mail application.

MARKING SCHEME
SECTION A (40 MARKS)
ANSWER ALL THE QUESTIONS FROM THIS SECTION IN THE SPACES PROVIDED
- One of the functions of an operating system is to control computer resources. State three resources under operating system control (3 marks)
Processor
Input/output devices
Application programs
Storage devices
Communication devices and ports -
- The figure below shows the relationship between tables in a database.
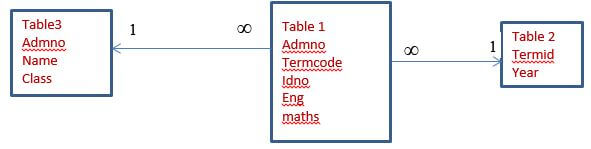
Identify two primary keys and two foreign keys used in the relationships (2 marks)
PK FK
AdmNo TermId
TermCode AdmNo
- Distinguish between bound and unbound controls as used in database forms (2 marks)
Bound controls are used to get data from a table or query while unbound controls do not get data from a table/query/link.
- The figure below shows the relationship between tables in a database.
- Explain why an impact printer is suitable for printing multiple copies (2 marks)
They have special hammers that produce characters on a piece of paper. And behind every paper, there is a coupon copy that produces characters on another paper.
- State any four examples of document readers (2 marks)
OBR
OMR
OCR
MICR -
- Define the term simulation (1 mark)
This is the process of creating a model of a real object/concept in order to experiment the behavior of a real object using a computerized model
- List two educational areas where simulation programs can be used (1 mark)
Training drivers
Training pilots
Training engineers
- Define the term simulation (1 mark)
- Explain two ways of protecting data and information against unauthorized access (2 marks)
-Password protection –allows the user to open/ modify file/doc
-Data encryption-only authorized user can decipher the code
-User and group permission to user- user access levels
-Firewalls- filters data and information exchanged between different networks
-Security monitors-keeps tracks of activities performed using computer systems e.g. CCTV
-Biometric security- only users whose attributes are identified can access
- Explain two characteristics of good information (2 marks)
-Accuracy- should be as close to the actual value as possible
-Timeliness- should be available when needed
-Relevance- should be useful in order to give out the expected output
-Completeness
- Explain three types of errors that are likely to exist in a program (3 marks)
-Syntax errors- errors as a result of incorrect use of a programming language e.g. spelling, incorrect punctuation, use of reserved words etc.
-Logical errors-errors that prevent the program from doing what it is expected to do
-Runtime errors- results in unexpected/ premature end of a program e.g. an attempt to divide a number by zero
- State two roles of a network admistrator (2 marks)
-Sets up a computer network
-Maintain and enforce security measures on the networks
-Monitor use of network resources
-Maintain and troubleshoot network related problems
- State three negative impacts of information communication technology on the environment (3 marks)
-The huge piles of garbage of dead computers and accessories causes pollution
-Massive extraction of mineral resources for making computer parts
-Energy consumption and radiation
-Disposal of nickel-cadmium laptop batteries contain cadmium which leaks to the underground water table
- Study the follow flowchart then answer the questions that flow.
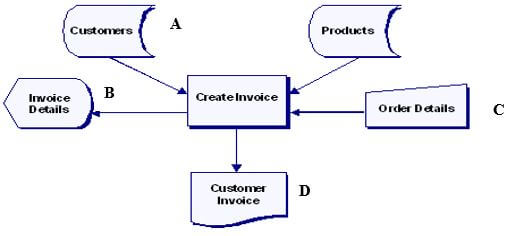
- Identify the type of flowchart represented by the flowchart in figure (1 mark)
System flow chart
- Name the flowchart symbols labeled A, B,C and D in the flowchart. (2 marks)
- Stored data
- Screen output/ display
- Manual input
- Document/report
- Identify the type of flowchart represented by the flowchart in figure (1 mark)
- Mary a computer student noticed that every time a person enters the computer lab, the computer screen flickered. Identify three reasons why the monitor might be flickering (3marks)
- There may be a loose connection to the computer hence flickering when touched
-Cables maybe laid on the pathway hence flickering when stepped on.
-Electrical interference from other electrical nearby devices
-
- state the importance of column breaks as used in a word processor (1 mark)
Used to enforce an end of a column to start/ move the cursor at the beginning of the next paragraph
- List any two line spacing specifications used in Ms- Word (1 mark)
-Single
-Double
-1.5
-multiple
- state the importance of column breaks as used in a word processor (1 mark)
- The first column in the table below contains the formula stored in cell C10 of a spreadsheet. Enter the formula as they would appear when copied to cell F15 of the same spreadsheet (2 marks)
FORMULA IN C10
FORMULA IN F15
=A5*B5
=D10*E10
=4*B$6
=4*E$6
-
- Differentiate between an analog and digital data signal (2 marks)
An analog data signal represents data that is continuous in nature while digital signal represents data that is non- continuous in nature - The government of Kenya is in the process of laying out fibre optic cables throughout the country. State three advantages of fibre optic cables (3 marks)
-Not prone to electromagnetic interference
-Supports a high bandwidth
-Low attenuation thus suitable for long distance transmission
-Smaller and lighter than copper cables
-Do not generate electrical signals thus can be used in hazardous places
- Differentiate between an analog and digital data signal (2 marks)
SECTION B( 60 MARKS)
ANSWER QUESTION 16 AND ANY OTHER THREE QUESTIONS FROM THIS SECTION
-
- Draw a program flowchart that would accept and their sum. If the sum is greater than 200, it adds 30 to the sum, otherwise subtracts 20 from the sum. The program should then display the results (7 marks)
- Study the pseudo code below and determine its output (3 marks)
STEP 1: T=0
M=0
K=1
STEP 2 M=M+T
T=T+5
K=K+1
STEP 3 REPEAT STEP 2 WHILE K<3
WRITE M, T
EXIT -
- List two benefits of using interviews as a method of fact finding (2 marks)
-Users can express their opinions in a detailed way
-Non- verbal communication can be observed
-Questions can be paraphrased for clarification
- Explain three types of system change over strategies (3 marks)
-Parallel- both the old and the new systems operate together for a period of time before the old system is discarded.-Direct- the old system is discarded and the new one implemented immediately-Phased- the old system is gradually replaced in stages by the new system-Pilot- a section of the organization runs the new system while the rest runs the old system.
- List two benefits of using interviews as a method of fact finding (2 marks)
- Draw a program flowchart that would accept and their sum. If the sum is greater than 200, it adds 30 to the sum, otherwise subtracts 20 from the sum. The program should then display the results (7 marks)
-
- state three functions of a database management system (DBMS) (3 marks)
- allows the user to add or delete records
-update or modify existing records
-organise data for easy access, retrieval and manipulation
-acts as an interface between the database and other applications
-enforce security for data in a database
-keep statistics of data items in a database
- if a database was to be created for a list, Tables, Forms, Queries and Reports are likely to be used. State the purpose of each of the objects (4 marks)
-Table- for storing data
-Forms- data entry, editing and viewing the records
-Queries-extracting data used on some criteria/ performing calculations
-Reports- creating summaries for data/ performing calculations
- The information below is maintained by Jessica Fruit store. Study it and answer the questions that follow:
Write down the query statements you can use to list the following;Product number
Product name
Qty in stock (kg)
Value per unit (ksh)
001
Peach
1000
200
002
Oranges
1200
200
003
Mangoes
1300
100
- Product names starting with letter P. (2 marks)
Like P* or P* in query design window - Value per unit below 200. (2 marks)
<200 in query design window.
- Product names starting with letter P. (2 marks)
- The following is a spreadsheet relating to a farmer (2 marks)
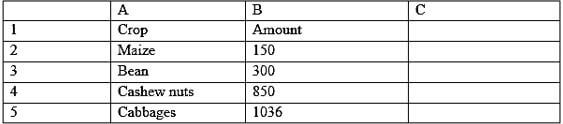
A function = IF (B2<200, “Not Viable”, IF (B2>300, “Moderate”, IF (B2>1000, “Viable”))). Give the appropriate result returned in cells C2, C3, C4 and C5
Name four data types used in spreadsheets. (2 Marks)1 Not viable 2 Not viable 3 Not viable 4 Moderate 5 Viable
-labels
- Values
- Formulae
- Functions
- state three functions of a database management system (DBMS) (3 marks)
-
- Explain the use of the following commands found in the spell check dialog box in reference to word processing (3 Marks)
i) Change – replace a word with a spelling error with the given suggestion
ii) Ignore once – leave a word with a spelling error without making any change
iii) Add – used to add a new vocabulary in a list of suggestions into
- State four font styles supported by Ms. Word (2marks)
- Bold
- Bold italics
- Italics regular
- Underline
- Work out the following binary arithmetic (2marks)
- 11101.00112 + 101.0112
11101.00112
+00101.01102
100010.10012
- 101001.101012-110.011012
101001.101012
000110.011012
100011.010002
- Using twos complement, perform the following calculation. (4marks)
2310 - 4110
2310 - 4110
23=000101112
41=001010012 1s complement=110101102
2s complement=110101112
23-41=000101112+110101112=111011102
{Decimal to binary conversions 1mark each (max 2)
1s complement ½ mark
2s complement ½ mark
Addition 1 mark}
- Convert 13.12510 to decimal. (2marks)
Whole number part
2
13
Rem
2
6
1
2
3
0
2
1
1
0
1
1310=11012
Therefore, 13.12510 = 1101.0012 ½ mark - A particular computer stores numbers in a single 8-bit word. How would it represent 0.312510? (2 marks)
0.3125 x 2 = 0.6250 0
0.6250 x 2 1.25 1
025 x 2 0.50 0
0.5 x 2 1.00 1
= 0.01012
- 11101.00112 + 101.0112
- Explain the use of the following commands found in the spell check dialog box in reference to word processing (3 Marks)
-
- Explain each of the following type of operating systems (4marks)
- Distributed
This is an operating system that manages a group of distributed computer system. Distributed computations are carried out on more than one machine.
- Multi-user.
A multi-user operating system is one that allows for multiple users to use the same computer at the same time and/or different times. Examples include UNIX, Linux, MAC OS and Windows Server 2003.
- Distributed
- List any two types of embedded operating systems used in modern cell phones (2marks)
-Android
-Symbian
-Windows
-FreeBSD
-Minix 3
- Most operating systems provide a file system. Mention any TWO file systems used in windows environment. (2 marks)
FAT (file allocation table)
FAT16
FAT32
NTFS (new technology file system)
- Define the term interactive data processing. (1mark)
In interactive data processing there is continuous dialogue between the user and the computer. As the program executes, it keeps on prompting the user to provide input or respond to prompts displayed on the screen.
- Explain why input screens are better data entry designs than entering data directly a table. (2 marks)
- Faster way of data entry
- One record can be viewed at a time.
- Data validation is possible
- One is able to compute data.
- State two likely causes of data and program loss in a computer system? (2 marks)
- Computer virus corrupting data and instructions
- Uneven power supply to system components
- Theft of data or programs
- Disk crash
- Explain the meaning of the following terms as used in data security (2marks)
- Fraud
use of computer to conceal information or cheat other people with the intention of gaining money or information - Alteration
the legal charging of data or information with the intention of misinforming authorized users or gaining
- Fraud
- Explain each of the following type of operating systems (4marks)
-
- The figure below shows an extract of an e-mail application.
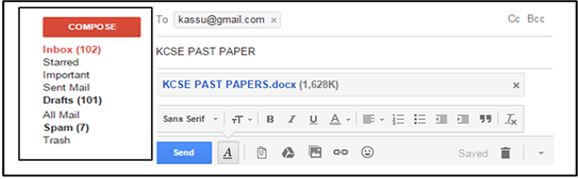
State what is meant by the following (3 marks)- Trash
Acts as a dust bin for your e-mail account where all deleted mails are stored before being permanently removed from the account
- Spam
This is a folder in your account where all junk and suspicious mails received are stored
- Inbox
This is a folder in your account where all genuine mails received are stored
- Trash
- Explain the following interactive sensory equipment used in virtual reality (2marks)
- Head gear
A device with tiny screens worn on the head, enable the weaver to view the virtual world.
- Body suit
Worn by the user, enable the wearer to explorer the virtual world
- Head gear
- Most computerized security systems make use of Biometric analysis, name three physical features of human beings that can be considered in this analysis (3marks)
- Finger prints
- Voice recognition
- Eye / facial recognition.
-
- Define the term networking topology (1mark)
Refers to the arrangement of the computers, printers and other equipment connected on the network
- Distinguish between logical and physical network topologies (2marks)
Logical (signal) topology deals with the way data passes from one device to the next in a network while physical topology refers to the physical arrangement (layout) of devices on the network
- Define the term networking topology (1mark)
- Explain the functions of the following network devices (4marks)
- Network interface card (NIC)
Creates a physical link between the computer and the transmission media
- Gateway
Provides access to a wide area network
- Bridge
Device that selectively determines segment where message is to be delivered - Repeater
Receives a weak signal cleans and amplifies it for transmission over the next position of the network
- Network interface card (NIC)
- The figure below shows an extract of an e-mail application.
Download Computer Studies Paper 1 Questions and Answers - Asumbi Girls Highschool Pre-Mock Exams May-June 2022.
Tap Here to Download for 50/-
Get on WhatsApp for 50/-
Why download?
- ✔ To read offline at any time.
- ✔ To Print at your convenience
- ✔ Share Easily with Friends / Students