Questions
INSTRUCTIONS TO CANDIDATES
- Answer ALL the questions in section A
- Answer question 16 (compulsory) and ANY OTHER THREE questions from section B.
SECTION A: (40 MARKS)
Answer ALL questions in the spaces provided
-
- Explain the emerging trends in microcomputer technology in relation to Size (1 mark)
- Name four categories of input devices (2 marks)
- State three ways in which computers have been used to fight the spread of corona virus in Kenya. (3marks)
- A Form four student wants to send a large document to a printer.
- State the name for the area of memory that the document is sent to immediately from RAM. (1 mark)
- As the printer runs out of paper during printing, the operating system sends a signal back to the computer to stop temporarily. Name this function of the operating system (1 mark)
-
- Give two advantages of the higher number of pixels per square centimeter. (1 mark)
- Differentiate between Data interface cable and power cable. (1 mark)
- Explain two differences between serial and parallel communication ports of a computer. (2 marks)
-
- What is line spacing as used in word processing? (1 mark)
- Describe any two line spacing specification used in Microsoft Word. (2 mark)
- Name the two documents used in mail merge. (1 mark)
- With reference to the concept of graphics as used in Microsoft word. Explain the difference between object linking and embedding? (1 mark)
- Who am I?
- Am is skilled in software/program development as per requirement and technical operations of Computer hardware. I also develop and update both system and application software together with the associated documentations. (1 mark)
- Am is skilled in designing computer hardware and also improves on existing ones. (1 mark)
- During the COVID 19 pandemic, the government advised the citizens to use electronic funds transfer and other popular mobile phone money transactions to make payments.
- State two ways how the above method of conducting business would help to curb on the spread of the disease. (2 marks)
- What is the meaning of Electronic Funds Transfer? (1 mark)
- Define the term dual booting as used in computing. (1 mark)
- Differentiate between cropping and grouping. (2 marks)
- Other than flow chart, state two other tools that can be used to represent an algorithm . (2 marks)
- Differentiate between a deadlock and interrupt as used in operating system. (2 marks)
-
- Securem is a company that deals with providing security services to its clients. Name any two Ways the company can protect its computer network from hackers. (2 marks)
- State four characteristics of a suitable password. (2 marks)
- During system development the system analyst should consider the correct requirement Specifications for the new system. State any four outcomes that may result from using incorrect requirement specifications. (2 marks)
-
- Define the term Computer Aided Design. (1 mark)
- List two advantages of using Computer Aided Design. (2 marks)
- Explain two arithmetic errors that may occur during computerized data processing. (2 marks)
SECTION B (60 marks)
Answer question 16 and ANY OTHER THREE questions from this section in the spaces provided.
- Give two examples of syntax errors in programming. (2 marks)
- With aid of a diagram, explain the “Repeat Until” construct as used in structured programming (3 marks)
- Classify the following programming languages according to their category: (3 marks)
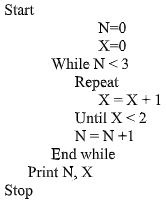
Programming language Category HTML JAVA JAVASCRIPT PASCAL VISUAL BASIC LISP - Study the pseudocode below and answer the questions that follow.
- What will be the output from the program (2 marks)
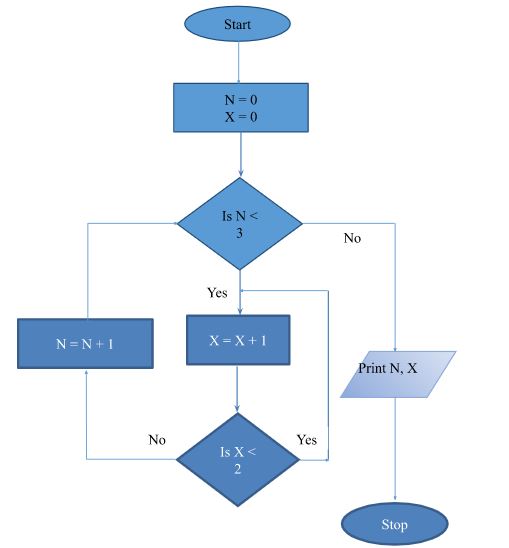
- Draw a flowchart that was used to come up with the following pseudo code (5marks)
-
- State the stage in system development life cycle where each of the following activities are
Carried out:- Identifying shortcomings of a system. (1 mark)
- Preparing the system migration plan (1 mark)
- Identifying the technologies that may be used in the proposed system. (1 mark)
- State and explain THREE components of an expert system. (3 marks)
- E-mail technology has become a very important part of today’s communication. Explain any three problems associated with using e-mail technology for communication. (3 marks)
- Sarafina wants to download her favorite movie from YouTube. State any three factors that may determine how long it will take her to complete the download. (3 marks)
- Most computerized security systems make use of biometric analysis. Name physical features of human beings that can be considered for this analysis. (3 marks)
- State the stage in system development life cycle where each of the following activities are
- The following Digital Club Member details were to be entered in a database: Name, Date of registration, Registration fee and Class.
- Prepare a suitable structure showing field names and their field types (4 marks)
Field data type Name Date of registration Registration fee Class - Name one other field that the Club Patron may need to add to uniquely identify the records (1 mark)
- Write the statement that can be used to select members of the class form 3. (2 marks)
Name Date of registration Registration fee Class Criteria/Expression - The following is an extract from a spreadsheet created to manage sales. Use it to answer the questions that follow.
A B C D 1 ITEM NAME UNIT PRICE UNITS SOLD 2 HDD 300GB 7 500 2 3 Optical Drive 4 500 8 4 DELL Latitude core i5 44 500 3 5 DDR4 8GB RAM 10 000 4 6 Lenovo Yoga Smart Tab 28 953 1 - Write a formula that will compute the number of items whose unit price whose price more than 10,000 (3 marks)
- If the formula =$B2*C$2 was placed in D2, state the output if copied to D3. (2 marks)
- Write the cell referencing used in c(ii) above. (1 mark)
- Write the data type that is stored in cell C5 and A6 respectively (2 marks)
- Prepare a suitable structure showing field names and their field types (4 marks)
-
- Define the term attenuation as used in networking and data communication. (1 mark)
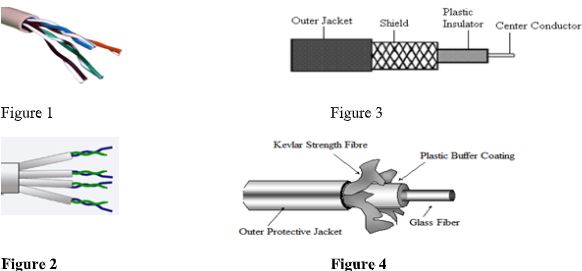
- The following are figures of networking cables. Identify each. (2 marks)
-
- Give two examples of network software (2 marks)
- In a network setup, list any two items that may be referred to as data terminal equipment.(2 marks)
- Explain the following terms as used in networking (4 marks)
- Remote Communication
- Distributed processing
- State four functions of a server in a network (4 marks)
-
-
- Define the term accreditation as used in education. (2marks)
- Explain two factors you would consider before enrolling for an ICT course in a College (2marks)
- Describe three guidelines that should be followed when conducting an interview during information gathering (3marks)
- Convert the following number systems (4 marks) 37.62510 to binary
- Using Two’s compliment, perform the following arithmetic operation leaving your answer in decimal.
3910-1910 (4 marks)
-
Marking Scheme
-
- Explain the emerging trends in microcomputer technology in relation to Size
- P PCs are becoming small and portable, e.g. personal Digital Assistant (PDA)
- Name four categories of input devices
- Keying in devices
- Pointing devices
- Scanning devices
- Automated method
- Explain the emerging trends in microcomputer technology in relation to Size
- State three ways in which computers have been used to fight the spread of corona virus in Kenya.
- Computers have been used to sensitize people on safety measures that help in preventing spread of virus
- For printing posters
- For conducting medical research in KEMRI
- For carrying out statistics for people infected with corona virus in Kenya in Kenya and comparing it with other countries (first
- A Form four student wants to send a large document to a printer.
- State the name for the area of memory that the document is sent to immediately from RAM
- Input buffer
- As the printer runs out of paper during printing, the operating system sends a signal back to the computer to stop temporarily. Name this function of the operating system Interrupt handling
- State the name for the area of memory that the document is sent to immediately from RAM
-
- Give two advantages of the higher number of pixels per square centimeter
- Higher screen resolution
- Displays of sharp & clear images
- The screen is able to display a higher number of different images
(first 2 correct @ 1mk, ½ mk each)
- Differentiate between Data interface cable and power cable
- Data interface cable -These are special cables that connect all the peripheral devices to the motherboard and the CPU. They transmit data signals and information to and from the devices
Power cable - Cable that supplies power to devices (correct @ 1mk)
- Data interface cable -These are special cables that connect all the peripheral devices to the motherboard and the CPU. They transmit data signals and information to and from the devices
- Explain two differences between serial and parallel communication ports of a computer
- Serial ports have 9 pins, while parallel ports have holes for 9 or 25 pins
- Parallel cables transmit several bits of data simultaneously, while serial cables transmit One bit at a tim
- -Serial cables are slower than parallel cable
- Serial cables allow for 2 ways communication (i.e. communication to and from the computer and the device connected to it) while parallel cables usually offer 1- way communication. (first 2 @ 2mks)
- Give two advantages of the higher number of pixels per square centimeter
-
- What is line spacing as used in word processing?
- The vertical distance between two text lines in a document (correct @ 1 mk)
- Describe any two line spacing specification used in Microsoft Word.
- Single space – accommodates the largest font in a line
- 1.5 line space- 1 ½ time that of single line spacing
- Double – twice that of single line spacing
- Exactly – a fixed line spacing that word does not adjust
- At least – the minimum line spacing that is needed to fit the largest font or graphic on the line.
- Multiple- a line spacing that is increased or decreased by a percentage that you specify (first 2 @ 2mks, each ½ mk)
- Name the two documents used in mail merge
- main document
- Data source
- With reference to the concept of graphics as used in Microsoft word. Explain the difference between object linking and embedding?
- In linking, the object imported can only be edited in the original application from which it was created.
- In embedding, the object imported becomes part of the current application and can be edited there.
(correct difference @ 2mk)
- What is line spacing as used in word processing?
- Who am i?
- Am is skilled in software/program development as per requirement and technical operations of computer hardware. I also develop and update both system and application software together with the associated documentations.
- -A Software developer/Engineer (correct @ 1mk)
- Am is skilled in designing computer hardware and also improves on existing ones.
- A Computer engineer (correct @ 1mk
- Am is skilled in software/program development as per requirement and technical operations of computer hardware. I also develop and update both system and application software together with the associated documentations.
- During the COVID 19 pandemic, the government advised the citizens to use electronic funds transfer and other popular mobile phone money transactions to make payments.
- State how the above method of conducting business would help to curb on the spread of the disease
- Instant – One receive s the money –During the lockdowns people were able to send financial support easily
- Used as a measure to quarantine or curb spread of COVID 19 which spreads easily through hands and infected items or surfaces
- Digital payments allow people to access goods and services while in quarantine or social distancing.
- digital payments were such an alternative to boosting or sustaining e-commerce in the country.
- Local Governments and well-wishers were able to fundraise and distributed vouchers
- Businesses experience some level of growth with e-commerce and online payments .
- What is the meaning of electronic funds transfer?
- EFT (electronic fund transfer) - us used to move money from one account to another. Or from case of mobile phone transactions .The transactions are completed electronically, and the two accounts can be at the same financial institution or different financial institutions. Term “EFT” is an umbrella term that covers a broad range of electronic payments
- State how the above method of conducting business would help to curb on the spread of the disease
- Define the term dual booting as used in computing.
- A dual boot is when you INSTALL two operating systems on one computer and being able to choose which one to boot (correct @1mk
- Differentiate between cropping and grouping.
- Cropping is removing unwanted parts of a graphics
- Grouping is combining more than one object to be manipulated as one (correct @ 2mks
- Other than pseudo code, state two tools that can be used to present an algorithm
- flow chart
- Decision Tables
- Decision Trees (any two @2mks)
- Differentiate between a deadlock and interrupt as used in operating system.
- Deadlock refers to a situation whereby a particular job holds a resource and refuses to release it yet it is requesting for a resource held by another job
- Interrupt is a break from the normal sequecial processing of instructions in a program
(Correct @2mks)
-
- Securem is a company that deals with providing security services to its clients. Name any two ways the company can protect its computer network from hackers.
- Log files
- Data encryption
- Use of password
- Firewalls (first 2 @2mks
- State Four characteristics of a suitable password.
- Easy to remember
- Hard to guess
- Should be a combination of letters and numbers
- Should be a minimum of 8 characters (first 4@½ mk
- Securem is a company that deals with providing security services to its clients. Name any two ways the company can protect its computer network from hackers.
- During system development the system analyst should consider the correct requirement specifications for the new system. State any four outcomes that may result from using incorrect requirement specifications.
- More costs than was projected
- The system will be delivered later than schedule
- The system will not meet user’s expectations
- The cost of maintaining and enhancing the system may be excessively high
- The system may be unreliable and prone to errors and downtime (first 4 @ 4 mk )
- Define the term Computer Aided Design.
- A system of programs and workstations used in designing engineering, architectural and scientific models ranging from simple tools to building. (correct @ 1mk)
- Explain two arithmetic errors that may occur during computerized data processing.
- Truncation error
- Rounding off error
- Overflow error (state @½ mk , explain @½ mk, total 1mk each)
-
- Give two examples of syntax errors in programming.
- Punctuation mistakes
- Improper naming of variables
- Wrong spellings of user defined and reserved words. (first 2@2mks)
- With aid of a diagram, explain the “Repeat Until” construct as used in structured programming
- the program first executes then tests the condition and continues looping until the condition turn to true
- The program tests and then executes until the condition becomes true
(diagram @1mk, correct explanation @ 1mk
- Classify the following programming languages according to their category:
Programming language Category HTML Web scripting JAVA OOP JAVASCRIPT Web scripting PASCAL 3GL VISUAL BASIC 4GL LISP 5GL -
- What will be the output from the program
- X - 4
N - 3
- X - 4
- Draw a flowchart that was used to come up with the following pseudocode
- What will be the output from the program
- Give two examples of syntax errors in programming.
-
- State the stage in system development life cycle where each of the following activities are carried out:
- Identifying shortcomings of a system.
- Problem definition
- Preparing the system migration plan
- Implementation stage (1mk)
- Identifying the technologies that may be used in the proposed system.
- system analysis(correct @1mk)
- Identifying shortcomings of a system.
- State and explain THREE components of an expert system.
- Knowledge base – stores knowledge inform of rules and facts concerning a certain subject of Interest
- Inference engine – Software which controls how knowledge is searched and accessed from the knowledge base
- User interface – A feature that enables the user to interact with the system
- E-mail technology has become a very important part of today’s communication. Explain any three problems associated with using e-mail technology for communication.
- Threat to privacy
- Messages can be sent to many people without their consent
- Email attachments can be sources of viruses
- Not available to all/technology illiteracy
- Emails can be unsolicited/spam mail
- Encourage illicit communication such as immoral behavior (first 3 @2mks each
- Sarafina wants to download her favourite movie from YouTube. State any three factors that may determine how long it will take her to complete the download.
- Other activities that may be running in the computer
- Bandwidth of the media used
- Size of the video
- Other restrictions enforced in the computer (first 3 @ 3mks)
-
- Eye pattern
- Finger prints
- Voice
- State the stage in system development life cycle where each of the following activities are carried out:
- The following Digital Club Member details were to be entered in a database: Name, Date of registration, Registration fee and Class.
- Prepare a suitable structure showing field names and their field types
Field data type Name Text Date of registration Date Registration fee Currency or Number Class Text - Name one other field that the Club Patron may need to add to uniquely identify the record
- Member Number
- Write the statement that can be used to select members of the class form 3 (2mks)
Name Date of registration Registration fee Class Criteria/Expression Form 3 -
- Write a formula that will compute the number of items whose unit price whose price more than 10,000
- =COUNTIF(B2:B6,”>10,000”) OR @COUNTIF(B2:B6,”>10,000”) OR +COUNTIF(B2:B6,”>10,000”)
(B2:B6) Argument range @1 mark
(>10,000) Criteria @ 1 mark
All Formula correct @ 1 mark
- =COUNTIF(B2:B6,”>10,000”) OR @COUNTIF(B2:B6,”>10,000”) OR +COUNTIF(B2:B6,”>10,000”)
- If the formula =$B2*C$2 was placed in D2, state the output if copied to D3 (2mks)
- Formula is =$B3*C$2 @ 1 mark
=4,500*2
= 9,000 @ 1 mark
- Formula is =$B3*C$2 @ 1 mark
- Write the cell referencing used in c(ii) above
- Mixed cell referencing
- Write the data type that is stored in cell C5 and A6 respectively
- C5-Value
A6- label
- C5-Value
- Write a formula that will compute the number of items whose unit price whose price more than 10,000
- Prepare a suitable structure showing field names and their field types
-
- Define the term attenuation as used in networking and data communication
- It refers to the weakening of signal strength as it progressively moves from one point to another on the transmission media
- The following are figures of networking cables. Identify each.
- Figure 1: Unshielded Twisted Pair (UTP)
- Figure 2: Shielded Twisted Pair (STP)
- Figure 3: Coaxial
- Figure 4: Fibre optic
-
- Give TWO examples of network software
- Network operating system
- Network protocols
- Give TWO examples of network software
- Explain the following terms as used in networking
- Remote Communication
- It involves transmission of data signals between two communication devices located at different geographical location, through which people can be able to share ideas over network
- Distributed processing
- This involves the subdivision of a process into several sub process then each sub process can be processed at a different site co-currently hence speeding up the entire process
- Remote Communication
- State FOUR functions of a server in a network
- It allows sharing a network printer
- It allows communication between the various workstations in a network
- It provides control access to available storage devices in network
- It allows sharing of communication. Files in the network
- It provides the transfer of files from one workstation to another workstation in the network.
- Define the term attenuation as used in networking and data communication
-
-
- Define the term accreditation as used in education.
- The process of recognizing an institution as being able to offer degrees and diplomas.
- Explain two factors you would consider before enrolling for an ICT course in a college.
- Cost.
- Job opportunities.
- Where the examinations offered are recognized.
- The organization offering the course.
- Define the term accreditation as used in education.
-
- be careful about body language, sitting arrangement, closeness etc
- avoid personal biases in your questions and perceptions
- interviewee must be informed in good time and topic communicated earlier
- Convert the following number systems
- 37.62510 to binary
- Using long division get the binary of 3710 =1001012
get the binary of the decimal by multiplying repeatedly by two i.e 0.62510=0.1012
Add the binary of the whole number and the decimal
1001012+0.1012=100101.1012
- Using long division get the binary of 3710 =1001012
- 37.62510 to binary
- Using twos complement, perform the following arithmetic operation leaving your answer in decimal notation
- 3910 – 1910
using long division get the binary of:
3910 = 1001112
1910= 100112
write the binary of 1910 in 8-bits 1910= 000100112
ones complement of the binary of 1910=11101100
twos complement ones complement =11101101
add the binary of 3910 to the twos complement of 1910
11101101
+0100111
(1)00010100 ignore the overflow
(1x24)+(1x22)=2010
- 3910 – 1910
-
Download Computer Studies Paper 1 Questions and Answers - Mathioya Mock Exams 2022.
Tap Here to Download for 50/-
Get on WhatsApp for 50/-
Why download?
- ✔ To read offline at any time.
- ✔ To Print at your convenience
- ✔ Share Easily with Friends / Students