SECTION A: 40 MARKS
Answer all the questions in this Section
- A sales man in Moyale uses Electronic mail to communicate with Head office in Nairobi. Mention three item that the Sales man must have to use this facility. (3marks)
- One of the functions of computers is to process and provide storage for information. Describe how doctors and nurses would benefit from the use of computers in hospitals (3marks)
- Distinguish between Simulation and Virtual reality (2marks)
- Mention three main components of an expert system (3marks)
- At times computer give unexpected results when performing operations in arithmetic. Explain what might have happened if the error message 'Arithmetic Overflow' appear on the screen (2marks)
- Antistatic Bag, Antistatic wrist member , screw driver and pliers are tools required during basic computer setup and cabling. Briefly describe the functions of Antistatic wrest member and pliers (2marks)
- James wanted to purchase genuine software to be installed in his personal computer. Name three items that must accompany the software to proof that the software is genuine, original and from a trustworthy source (3marks)
- State the difference between Make table Query and Append query in Databases (2marks)
- Mention three causes of syntax error in a computer program (3marks)
- Tom a student from Klemo Secondary school sat for his KCSE in the year 2018 and passed well but did not join the university due to financial problems. In the year 2020 he was advised by a friend to a pursue course under the TVET program. List any three ICT related courses that Tom may apply for (3marks)
- Kipasi Secondary school upgraded their computer lab by installing modern computers. Mention how the school management will control theft of hardware and software from the lab (3marks)
- Explain the following terms as used in Desktop publishing
- Overflow (1mark)
- Master page(1mark)
- Mention three sources of graphic objects with reference to Word processors (3marks)
- Dama a secretary at Jusa Secondary caries out her daily duties using computers and suffered from wrist strain. State two ways she would reduce wrist strain (3marks)
- Mr. Baraka games teacher at Chianda High School wants to invite several school for the hockey tournament. He was advised to use mail merging technique to create invitation letters for the respective schools identified. State three benefits of this technique (3marks)
SECTION B: 60 MARKS
ANSWER QUESTION NUMBER 16 ANY OTHER THREE QUESTIONS FROM THIS SECTION
-
- Mention three limitations of machine language (3marks)
- Describe three methods usually used by a computer programmer to test a program (3marks)
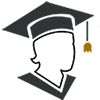
- Study the following pseudo and answer the questions that follow
1. Start
2. Set count=0
3. If count is less than 5 do
4. Get value 1 and value 2
5. If value 1 > Value2 Then
6. Maximum =Value 1
7. Else If Value 1<Value 2 Then
8. Maximum =Value 2
9. Else Go to 10
10. Display Maximum
11. Get the count and add one
12. Stop - State the purpose of the pseudo code (2marks)
- Draw a flowchart equivalent to the pseudo code (7marks)
-
- Give two reasons to justify the use of binary number system in computing (2marks)
- Convert
- 110.1012 to decimal (2marks)
- 1AH to Octal (2marks)
- Using twos compliment show how the arithmetic below could be carried out on a eight bit notation computer (+4610 )+(-2910) (3marks)
- Get the value of X2 in this expression below (3mark)
X2 + 78 = 9H - 11012 is a binary representation of a negative number. Workout the likely positive equivalents in base ten (3marks)
- Student database comprises of students details table and fee received.
Students' Details Table
First Name Middle Name Admission Number Course Code
Fee Received table
Date Amount ReceiptNo Mode of Payment - State the primary key for each table (2marks)
- Give the most appropriate data-type for Receipt. No and Mode of payment (2marks)
- Suggest how the date column can be validated to accept today's and earlier dates only (1mark)
- Describe how a relationship between the two tables can be established (3marks)
- A student was typing a document using word processor.
- She typed the word school as SHOOL. Describe how she would correct the error (2mark)
- When she tries to type letter C between letter S and H, letter H was deleted which to her was wrong. Explain the cause of this problem (2marks)
- Mention any three formulas that be added to Ms-Word table to perform simple calculations (3marks)
- Student database comprises of students details table and fee received.
-
- List three approaches used in Rapid Application Development during system development(3marks)
- What is system entropy (1mark)
- Explain four factors to consider when designing a file during requirement specification (4marks)
- Briefly describe three types of change over strategies a system analyst may adopt during implementation (3marks)
- State the difference between Bcc and Cc as used in email and Internet (2marks)
- State the function of each of the following feature with regard to email
- Draft
- Trash
-
- With reference to Operating System explain the following terms
- Error handling (1mark)
- Multitasking (1mark)
- Interrupt handling (1mark)
- Kingjames saved a document in his computer during the lesson. At the end of the lesson the teacher instructed him to delete the document, Kingjames looked for the document and was not able to locate the document. Describe three parameters that would help located the document (3marks)
- State three functions of a recycle bin (3marks)
- Give IS unit for measuring the following
- Memory (1mark)
- Processor speed (1mark)
- Describe four functions of electronic spreadsheet (4marks)
- With reference to Operating System explain the following terms

Marking Scheme
| Q | Description | Marks Awarded | ||||||||
| 1. |
A sales man in Moyale uses Electronic mail to communicate with Head office in Nairobi. Mention three item that the sales man must have to use this facility
|
Award 1 mark each max 3 | ||||||||
| 2. |
One of the functions of computers is to process and provide storage for information. Describe how doctors and nurse would benefit from the use of computers in hospitals.
Note that full marks will be awarded when the candidate includes the technology without technology award zero |
Award 1 mark each max 3 | ||||||||
| 3. | Distinguish between Simulation and Virtual reality Simulation is the science of representing the behavior of a real life situation by using computerized model while Virtual reality refer to a condition in which a person becomes psychologically immersed in an artificial environment generated by a computer |
Award 1 mark each max 3 | ||||||||
| 4. |
Mention three main components of an expert system
|
Award 1 mark each max 3 | ||||||||
| 5. | At times computer give unexpected results when performing operations in arithmetic Explain what might have happened if the error message "Arithmetic Overflow appear on the screen .
|
Award 2marks max 3 | ||||||||
| 6. | Antistatic Bag, Antistatic wrist member, screw driver and pliers are tools required during basic computer setup and cabling. Briefly describe the functions of Antistatic wrest member and pliers
|
Award 1mark each max 2 | ||||||||
| 7. | James wanted to purchase genuine software to be installed in his personal computer. Name three items that must accompany the software to proof that the software is genuine, original and from a trustworthy source
|
Award 1mark each max 3 | ||||||||
| 8. | State the difference between Make table Query and Append query in Databases.
|
Award 2marks max 2 | ||||||||
| 9. | Mention three causes of syntax errors in a computer program
|
Award 1mark each max 3 | ||||||||
| 10. | Tom a student from Klemo Secondary school sat for his KCSE in the year 2018 and passed well but did not join the university due to financial problems. In the year 2020 he was advised by a friend to a pursue course under the TVET program. List any three ICT-related courses that Tom may apply for
|
Award 1mark each max 3 | ||||||||
| 11. | Kipasi Secondary school upgraded their computer lab by installing modern computers. Mention how the school management will control theft of hardware and software from the lab
|
Award 1mark each max 3 | ||||||||
| 12. | Explain the following terms as used in Desktop publishing .
|
Award 1mark each max 2 | ||||||||
| 13. | Mention three sources of graphic objects with reference to Word processors
|
Award 1 mark each max 3 | ||||||||
| 14. | Dama a secretary at Jusa Secondary carries out her daily duties using computer and-suffered-from-wrist-strain-State-two-ways-she-would-reduce wrist pair
|
Award 1 mark each max 3 | ||||||||
| 15. | Mr. Baraka games teacher at Chianda High school wants to invites several schools for Hockey tournament. He was advised to use mail merging technique to create invitation letters for the respective schools identified. State three benefits of this technique
|
Award 1 mark each max 3 | ||||||||
|
16. |
|
Award 1 mark each max 3 Award 2marks max 3
|
||||||||
| 17. |
|
Award 1mark each max 2
M1 1mark A 1mark
M1 1mark A 1mark
M1 1mark
M1 1mark
Award 1mark each max 3
|
||||||||
| 18. |
|
Award 1mark each max 2 Award 1mark each max 2 Award 1mark each max 1
|
||||||||
| 19 |
|
|||||||||
Download Computer Studies Paper 1 Questions and Answers - Maranda Post Mocks 2020/2021.
Tap Here to Download for 50/-
Get on WhatsApp for 50/-
Why download?
- ✔ To read offline at any time.
- ✔ To Print at your convenience
- ✔ Share Easily with Friends / Students